What is Disassembly?
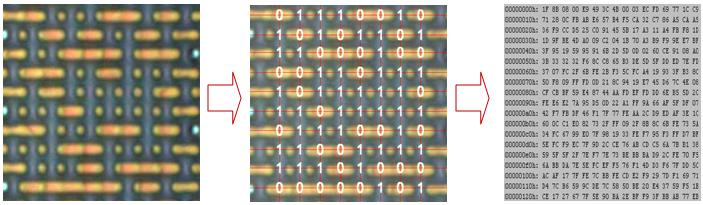
MCU disassembly is to decompile the BIN file or HEX file read from the MCU into an assembly language that engineers can understand. Disassembly is often required when there is no source file and the program needs to be changed, or code reverse engineering. This is a very professional technology. The reversed assembly needs to be 100% accurate, and a byte appears. If there is any error, then the reversed assembly file is meaningless.
The engineer must be able to understand the assembly file after disassembly, which requires the engineer to be very proficient in this series of single-chip microcomputers, and to be familiar with assembly language, reverse thinking, and electronic technology. etc. have very solid skills. We will import the disassembled file into the compilation environment to recompile and verify, and then compare the generated HEX with the original BIN file before disassembly to ensure that the disassembled code is completely correct.
The Purpose of Disassembly
Disassembly is not the goal, modifying the program is the ultimate goal. We have an experienced reverse engineering team that can help you solve various problems, such as removing program soft encryption, removing ID encryption, removing external encryption chips, and modifying time limits , modify the number of times limit, modify the interface LOGO, modify the machine serial number, add new functions. Modifying or adding new functions with only BIN files and HEX files is a very technical thing. It requires engineers to fully understand the disassembled code. Adding new functions without affecting the original functions is very important for customers’ product upgrades, so that your decrypted products are better than blue.
Applications of Disassembly
Electronic products are becoming more and more strict in soft encryption, and various encryption methods have emerged, among which ID encryption is the most common. Many single-chip microcomputers have unique ID numbers in the world, such as STM32. We have extensive experience in this area and can crack the ID encryption of electronic products without affecting the original function.
In addition to ID encryption, there are various other encryption methods on the market, as well as various dedicated encryption chips. However, the idea of encryption is still the same, that is, to verify the legitimacy of products. Now the more popular encryption algorithms are: SHA-1 message digest encryption algorithm; DES symmetric encryption algorithm; AES advanced encryption algorithm; RSA public key encryption algorithm, etc. Many encryption chips have integrated DES encryption module. We are proficient in the encryption ideas of various popular encryption algorithms above, and have unique solutions to various encryption schemes, including the most difficult encryption method to transplant key algorithms to smart card chips.
Disassembly tools
There’re many disassembly tools such as: OD, IDA Pro, radare2, DEBUG, C32, etc.
What can we do for you?
If the decrypted product will display the original serial number, some will also bind the serial number to the machine function. After the serial number is modified, even the function of the machine is abnormal. Many customers often delay for a long time because of this problem. The product cannot be brought to market. We have solved many similar problems for our customers and have accumulated rich experience in this area.